Last Updated November 20, 2025
A report shows that more than 60% of organizations surveyed experienced a cyber incident linked to a third party. To figure out whether a third-party vendor can keep your company’s data locked down, you need to ask a targeted set of vendor security questions that reveal how they handle cybersecurity risks under the hood. In this post, we’ll show you a vendor security questionnaire that helps you get a clear picture of their security practices and spot any red flags before they backfire.
Short on time? Get our vendor security questionnaire template
Content Snare is here to help you create your next vendor risk assessment questionnaire. Sign up to access our built-in vendor risk management questionnaire template. It’s ready when you are.
What questions should I be asking in a vendor risk assessment questionnaire?
In our experience, it’s best to keep questionnaires short and sweet if you want people to stay focused while filling them out. However, when it comes to internet security, cutting corners just isn’t an option, which is why we’ve provided an extensive list of critical questions below to ensure you cover all of the bases.
| Note: Screenshots you’ll see below are from Content Snare’s built-in vendor security questionnaire. |
Privacy and Security of Information
The first section will start to shed some light on how the vendor manages privacy and security and, of course, give you an indication as to whether this vendor’s policies are up to scratch or potentially risky.
- Does your organization process personally identifiable information (PII) or protected health information (PHI)?
- Does your organization have a security program?
- If so, what standards and guidelines does it follow?
- Does your information security and privacy program cover all operations, services and systems that process sensitive data?
- Who is responsible for managing your information security and privacy program?
- What controls do you employ as part of your information security and privacy program?
- Please provide a link to your public information security and/or privacy policy.
- Are there any additional details you would like to provide about your information security and privacy program?
Physical and Data Centre Security
This section focuses deeply on the environmental and physical factors relating to the security of data. That way, you can assess every aspect of the vendor’s situation and identify further possible risks unrelated to the previous section.
- Are you in a shared office?
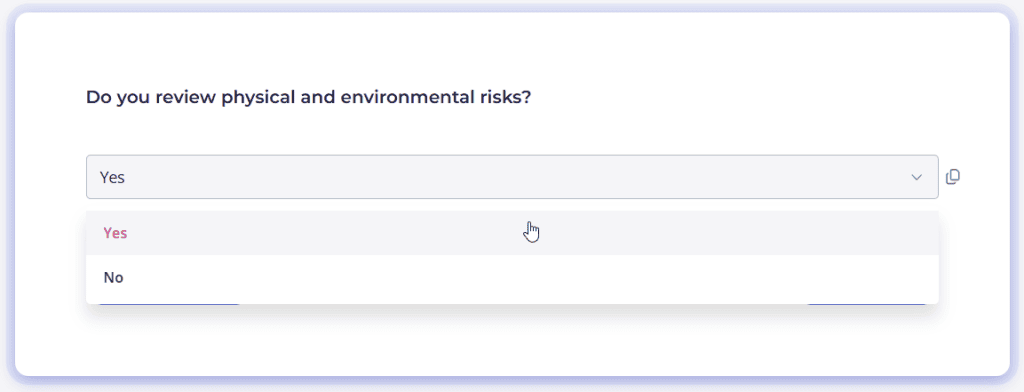
- Do you review physical and environmental risks?
- Do you have procedures in place for business continuity in the event that your office is inaccessible?
- Do you have a written policy for physical security requirements for your office?
- Is your network equipment physically secured?
- What data center providers do you use, if any?
- How many data centers store sensitive data?
- What countries are data centers located in?
- Are there any additional details you would like to provide about your physical and data center security program?
Web Application Security
The most lengthy by far, this section is a lifesaver when it comes to evaluating the security of the vendor’s web application. These questions will allow you to explore the full spectrum of said application.
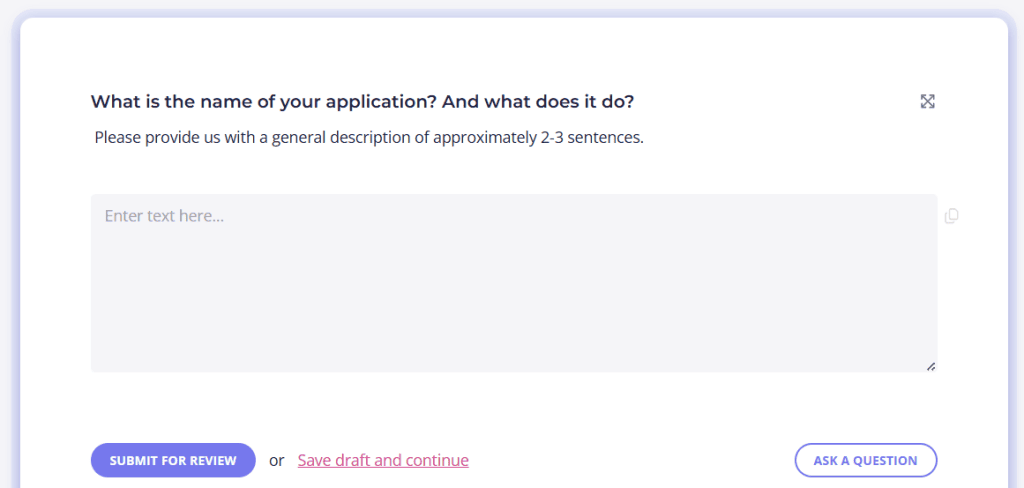
- What is the name of your application? And what does it do?
- Do you have a bug bounty program or other way to report vulnerabilities?
- Does your application have a valid SSL certificate to prevent man-in-the-middle attacks?
- Does your application require login credentials?
- How do users get their initial password?
- Do you have minimum password security standards?
- How do you store passwords?
- Do you offer single sign-on (SSO)?
- How can users recover their credentials?
- Does your application employ a defence in depth strategy? If so, what?
- How do you regularly scan CVE for known vulnerabilities?
- How do you do quality assurance?
- Do you employ pentesting?
- Who can we contact for more information related to your web application security?
Infrastructure Security
Finally, all things infrastructure! Learning about the vendor’s infrastructure is the icing on the cake that’ll help you make that final decision as to whether the vendor’s security measures are sufficient or not.
- Do you have a written network security policy?
- Do you use a VPN?
- Do you employ server hardening?
- How do you keep your server operating systems patched?
- Do you log security events?
- What operating systems are used on your servers?
- Do you backup your data?
- How do you store backups?
- Do you test backups?
- Who manages your email infrastructure?
- How do they prevent email spoofing?
- How do you protect employee devices from ransomware and other types of malware?
- What operating systems do employee devices use?
- Are employee devices encrypted?
- Do you employ a third-party to test your infrastructure security?
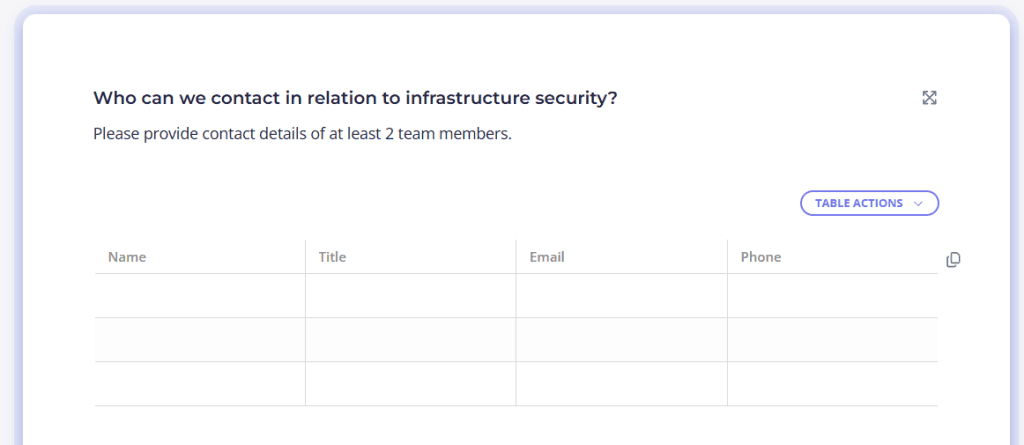
- Who can we contact in relation to infrastructure security?
What kind of breaches will a vendor risk assessment questionnaire protect me from?

Yipee! Your vendor risk assessment questionnaire is up, running and ready to be sent to any third party vendors.
However, in order to shed some light on exactly what breaches the questionnaire will help protect you from, let’s go through three of the most common and undesirable internet security breaches that thousands of technology companies are confronted with every year.
Physical breaches
Physical breaches involve losing control over sensitive data directly, often through human error, theft and other various environmental concerns.
Examples of circumstances leading to physical breaches include:
- An employee sending the information to an incorrect recipient
- An insider threat actor sending the trade secrets to competitors
- A robbery occurring inside the organisation’s premises
- An employee leaving a confidential file open on their computer at their desk
- An employee stealing the information to later sell or use in another manner for personal gain
Phishing attacks
A cybercriminal’s end goal is often to access restricted and personal data in an unauthorised manner in order to use said data to threaten people for ransomware. This is commonly achieved through launching phishing attacks to trick employees into clicking on dangerous links and/or downloading malicious resources. Does that ring a bell?
Most people have experienced some type of phishing attack in their lifetime but, with the wealth of knowledge available on the internet about such malicious links and downloads, we know more and more about how to differentiate the fake from the credible. However, on the occasions where the individual does click on any links, the execution of the malware can bypass security controls, allowing access into the system and to unauthorised data.
Password breaches
Newsflash! Passwords can be stolen, lost or guessed a hell of a lot more easily than you would think, especially given the plethora of password breaches that have occurred in the past.There are millions of leaked credentials available on the internet and it doesn’t take much searching to find them.
For this reason, those still relying upon passwords such as ‘Password’ or ‘123456’ are incredibly vulnerable to this type of attack. After having entered an account, the hacker will then be able to steal, alter or delete the desired files and data.
Which tool should I use to create my vendor questionnaire?
After you’ve collated your list of vendor questions, you’ll have to think carefully about which tool you’re going to use to create the assessment questionnaires that are going to be sent to potential vendors. Whilst several seemingly tempting options may surface following a Google search, it’s important to be aware of the many limitations present in the majority of questionnaire and form creation tools:
- No progress auto-saving
- Longer forms tend to be laggy
- No comprehensive vendor security questionnaire
- User-unfriendly design
This is why online tools like Content Snare exist, providing you with a broad range of features whilst remaining easy to use.
Fully editable vendor security questionnaire template
Content Snare gives you a vendor security questionnaire template you can tweak to your heart’s content. You can change, remove, or add questions (or entire pages and sections) so the whole thing fits your exact process. It’s a great way to hit the ground running without reinventing the wheel. Here’s how DFK Hirn Newey’s Hannah Olson explains it:
“The questionnaires gave me good insights on what I could be asking. I was able to ask more relevant questions than I would usually ask before. I also learned to ask clearer questions.”
Automatic reminders
Automatic reminders make sure vendors don’t leave your questionnaire gathering dust in their inbox. You can stick with the default reminder schedule or tailor it to whatever works best for your communication style. It’s a simple way to keep things moving without chasing people up manually.
A range of field types
With 30+ field types, you can ask any kind of question without jumping through hoops. For instance, your vendors can upload files, choose from dropdowns, fill in text fields, and even complete ID verification. It keeps responses consistent and easy for everyone involved.
Auto-save progress
Content Snare auto-saves every entry on the go, so no one loses their hard work if they step away or hit the wrong button. Vendors can pick up right where they left off without skipping a beat. This takes a load off their mind (and yours).
Military-grade security
Your data stays safe behind the kind of security controls you’d expect from a top-tier provider. Content Snare is backed by an ISO 27001 certification, so you know the platform isn’t cutting any corners. It’s one less thing to worry about in your work.
Avoid bottlenecks with our vendor security questionnaire template
Content Snare is here to ease the stresses of vendor risk assessment questionnaires. Sign up to access our vendor questionnaire template. It’s ready when you are.
Types of vendor security questionnaires you can build with Content Snare
Content Snare helps you build all types of vendor security questionnaires. For instance, you can stick to industry-standard frameworks or create something more tailored to your internal risk processes. The bottom line is that our platform gives you the flexibility to mirror well-known assessments while still customizing them to suit your exact needs.
Here are some of the more common types of vendor risk assessment questionnaires:
- Consensus Assessment Initiative Questionnaire (CAIQ): This is a standardized set of questions from the Cloud Security Alliance to assess a vendor’s cloud security posture.
- Vendor Security Assessment Questionnaire (VSAQ): Google’s modular questionnaire for evaluating a vendor’s security controls.
- Standardized Information Gathering Questionnaire (SIG): It’s an industry-recognized questionnaire that digs into privacy, cybersecurity, and risk management practices.
- Custom vendor security questionnaire: You’re free to create your own blend of compliance checks and technical questions.
No matter which format you choose, Content Snare makes it easy to build and manage your questionnaires without all the usual headaches.
FAQ
What is a vendor security questionnaire?
A vendor security questionnaire is a structured set of questions used to assess how a third-party vendor manages security and risk. It helps your organization evaluate whether a vendor’s systems and controls meet your security requirements before sharing any sensitive data.
Can I customize the vendor security questionnaire inside Content Snare?
Yes, Content Snare allows you to customize every part of your vendor questionnaire, from individual questions to entire sections or pages. You can create something simple or build a full-scale assessment tailored to your risk program.
How often should vendor security questionnaires be updated or reviewed?
Most companies review and refresh their vendor questionnaires once a year. They do it because security threats evolve quickly, so updating questions regularly guarantees you’re still assessing the risks that matter most.
How does Content Snare make vendor risk assessment questionnaires easier to manage?
Content Snare optimizes the entire workflow with features like automatic reminders, auto-save progress, flexible field types, and built-in templates. It keeps vendors on track while helping you collect accurate information without all the back-and-forth.


I would like to get more information about your Vendor Risk Questionnaire please
Hi Maria. Our questionnaire can be viewed on the templates page or inside your Content Snare account after signing up for a trial